Risk Analysis Based on IT-Grundschutz#
The required information is partly based on data that needs to be additionally documented, and partly on data already collected as part of the Procedure with VIVA according to BSI standard 100-2.
Identifying threats#
When assigning modules to a target group, not only measures but also threats belonging to that module are taken into account. Additional threats can be added, and existing ones can be modified or deleted. This is done within the assigned modules. (See BSI standard 100-3, chapters 3 and 4.)
Evaluating threats#
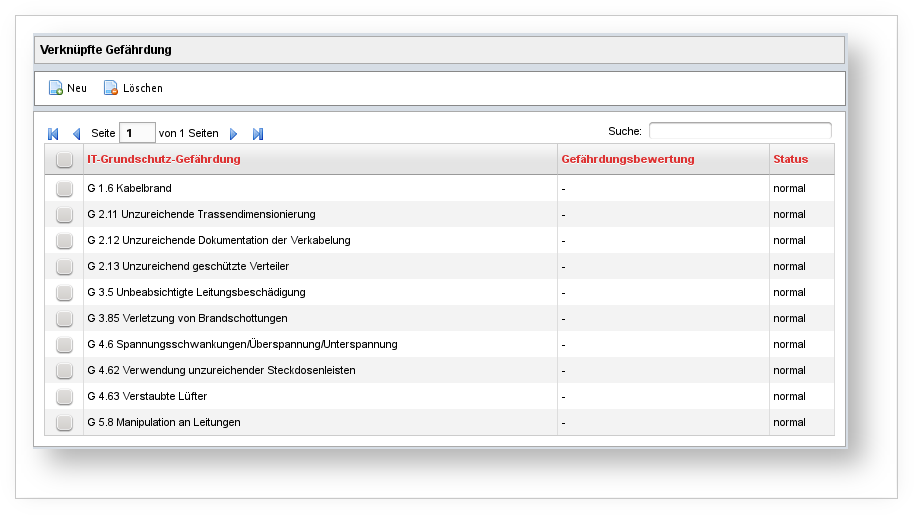
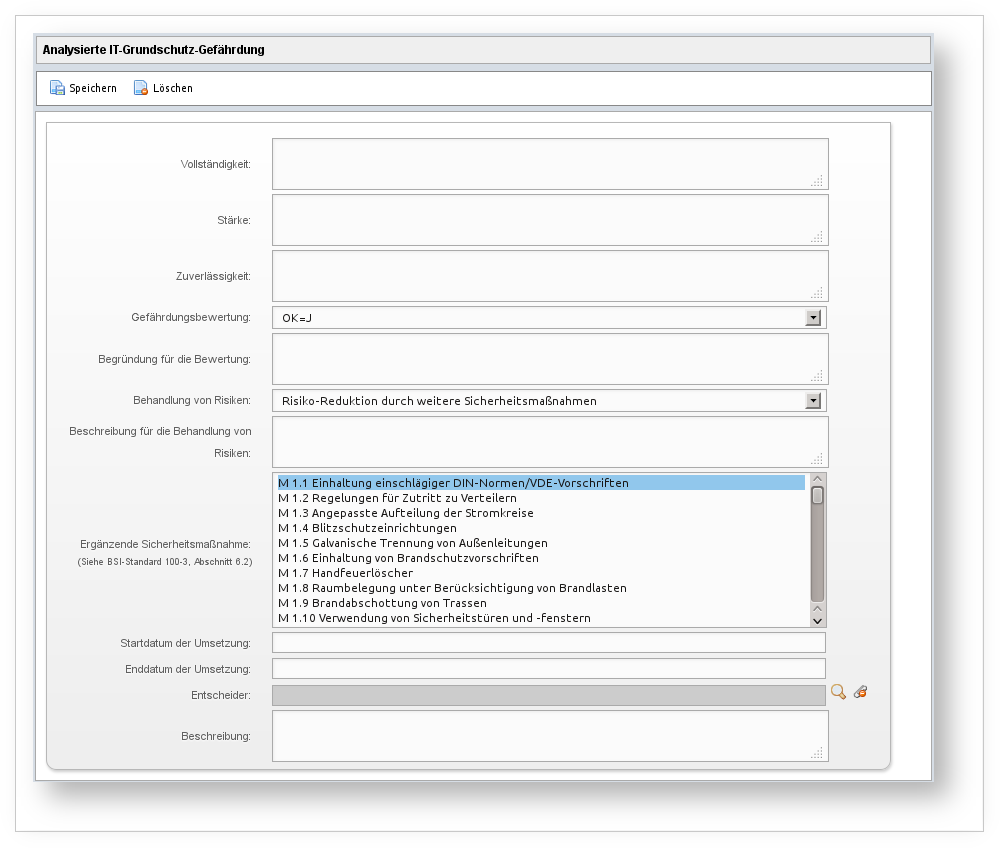
The evaluation of threats (see BSI standard 100-3, chapter 5) is documented within the linked threats -- found under Information Domain → Target Group → Assigned Module → Linked Threat.